It’s May 4, 2000, exactly 26 years ago today, and a guy named Onel de Guzman in Manila is seething because his thesis had just been rejected. So he’s reaching out to his friends and acquaintances and sending out emails from his Microsoft Outlook.
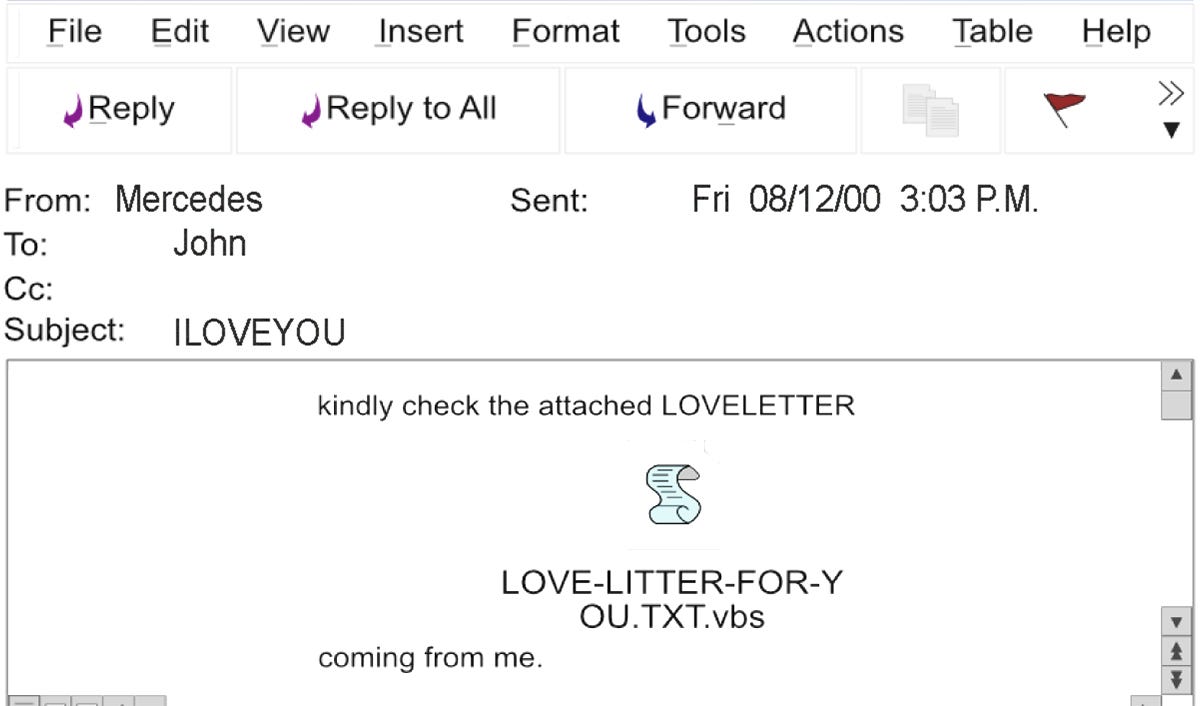
Subject line: I love you.
Message: “kindly check the attached love letter coming from me.”
Attachment: LOVE-LETTER-FOR-YOU.TXT
This seems like quite a sweet, benign email from a friend or a guy you are flirting with. It looks harmless and personal, so people click and open the attachment. And just like that, on that simple day, that simple email turned out to be one of the most famous cyberattacks in history, infecting over 50 million computers and costing about $5.5 to $8.5 billion to recover.
To this day, it remains one of the most famous examples of how hackers exploit human emotions, curiosity, and familiarity, and unfortunately, it continues to be one of the most complex attack surfaces for cybersecurity professionals to deal with.
But let’s bring it back for a second.
The moment the attachment is opened, the ILOVEYOU virus detonates. It overwrites files, it harvests passwords, then it escalates. It pulls the victim’s contact list and sends itself to everyone they know.
It multiplies exponentially. If one person has 50 contacts, all 50 receive the email from someone they know, and those 50 people then have thousands of contacts. Thousands turn into millions, and within hours, it goes global.
Because it spreads through a trusted email, it is opened by people inside corporations, governments, and military networks.
Users see an attachment, LOVE-LETTER-FOR-YOU.TXT, but it is actually LOVE-LETTER-FOR-YOU.TXT.vbs. They think it is a text file. It is not. It is executable code, and those three letters at the end are doing all the damage.
The virus becomes unstoppable because there is no rate limit on email sending, no modern spam filters at the time, and no attachment sandboxing. It spreads instantly and turns every infected user into an attacker.
(I promised you I’d teach cybersecurity in human language that doesn’t overwhelm you. But I also don’t want to be a jerk and throw around unexplained tech jargon, so I’ll drop in little explanations here and there, if that’s okay with you.)
VBS stands for a Visual Basic Script. It is a scripting language created by Microsoft. It can modify files, grab passwords, and send itself to everyone you know while you’re still thinking you just opened a love letter from a crush.
And sandboxing is exactly what it sounds like. You box the problem before it puts you in one. You take a suspicious file and isolate it in a controlled environment.
At its core, that “file” is code. In a sandbox, you allow that code to execute in a restricted, isolated runtime so you can observe its behavior without exposing your system. It runs with tightly scoped permissions, limited access to the filesystem, and controlled or blocked outbound connections. Everything it tries to do is monitored to prevent data exfiltration, etc.
Today sandboxing is a standard practice in cybersecurity, and a non-negotiable protocol, and most modern email systems automatically sandbox attachments.
That is one of the main reasons attacks like this no longer spread at that same chaotic, overnight global scale. They cannot easily access your contacts or propagate outward in seconds the way they did in 2000. That said, we’re far from in the clear. The original malware may be outdated, but the tactic is very much alive. Hackers rely on the same core trick: getting users to click before they think.
Modern attacks are no longer dependent on exploiting software vulnerabilities alone, they exploit decision-making under trust and urgency.
This is called phishing.
Phishing is a form of social engineering where attackers use digital communication channels, like email, SMS, voice, or legitimate-looking platforms, to impersonate trusted entities and manipulate users into disclosing sensitive information or performing high-risk actions. Those actions can include entering credentials into adversary-controlled infrastructure, approving authentication requests, downloading malicious payloads, or initiating financial transactions.
What makes phishing particularly effective is that it bypasses traditional technical defenses. There is no exploit to patch when a user voluntarily hands over access. The attack succeeds because it aligns with expected behavior, trusted branding, familiar workflows, and time pressure.
Some of the most common types of phishing attacks today are:
Business Email Compromise (BEC):
An attacker impersonates a trusted entity, often an executive or vendor, to manipulate the recipient into making financial transactions or disclosing sensitive business information. These attacks typically avoid obvious malicious links or attachments and rely on credibility and urgency.
An example of this would be receiving an email that appears to come from CEO stating:
“I need you to urgently process a wire transfer for a confidential acquisition. I’m in meetings all day, so handle this immediately and don’t delay.”
This tactic relies on urgency, authority, and isolation to bypass normal verification processes. It has been highly effective and has resulted in hefty financial losses,
Spear Phishing:
A highly targeted phishing attack directed at a specific individual or group. The message is tailored using personal or organizational context, making it appear to come from a legitimate and trusted source.
Good example for this would be Jason Knauf, CEO of EarthshotPrize emailing you saying:
“Hi Stacey, following yesterday’s Earthshot briefing, please re-authenticate your account to access updated documents.”
It references real events. The login page looks flawless. At a minimum, you’ll be prompted to enter your username and password, and more often than not, additional identifiable details. And given how careless and lazy people can be, those same login details are often reused across multiple platforms, including banks and personal email.
Whaling:
A specialized form of spear phishing that targets senior executives or high-value individuals. The objective is usually access to confidential data, financial assets, or strategic systems.
An example of this would be an email landing in Prince Willa’s inbox from his law firm Mishcon de Reya.
Text reads:
“Urgent: Legal notice regarding international media claims that you made your brother slurp from a doggie bowl. He alleges a catastrophic brain injury to his already pea-sized brain. Immediate executive review required.”
There will be an attachment. It looks official. It sounds official. The stakes feel sky-high. If Willa clicks it, game over.
A threat actor now has a foothold to lock down systems, hold policy and infrastructure hostage, demand ransom, and siphon whatever private data they can reach from William’s device.
Vishing (Voice Phishing):
The use of phone calls or voice-based communication, including VoIP, to impersonate legitimate entities and extract sensitive information such as credentials or financial details.
Vishing is only getting more dangerous with AI. Attackers can now clone voices, mimic tone, and recreate highly believable scenarios using publicly available data, videos, and even short audio clips.
This is why I strongly recommend having a shared family verification code or phrase. If someone calls claiming to be a loved one in distress, especially in high-pressure situations like a supposed kidnapping or accident, and the voice sounds exactly right, that alone is no longer proof. AI can replicate that. A private, pre-agreed phrase known only within your family creates a layer of verification that is far more difficult to fake.
Smishing (SMS Phishing):
Phishing conducted via text messages. Attackers use urgency, links, or impersonation to trick users into revealing information or clicking malicious URLs.
A very common entry point for these scams is the “wrong number” text. It looks harmless on purpose.
You get a message from an unknown number that sounds completely normal:
“Hey, how are you?”
“Can’t wait to see you tomorrow.”
“Long time no see.”
It’s designed to feel familiar enough that you engage. Most people respond with something like, “Sorry, who is this?” or “You have the wrong number.” That’s exactly what the attacker wants.
Your reply does one thing: it confirms your number is active and monitored by a real person. That validation is valuable. Once confirmed, your number can be added to lists for spam campaigns, phishing attempts, and more targeted social engineering.
The correct response is to not engage.
If you don’t recognize the number, delete the message.
If it actually is someone you know using a different number, they will find another way to reach you, usually by calling or contacting you through a known channel.
This is one of those small habits that makes a disproportionate difference. Treat unknown inbound messages as untrusted by default.
Unfortunately, we still don’t have strong user-facing defenses against these types of attacks. Tech leaders would argue that they have invested heavily in securing systems, but they have certainly failed to invest in the person using them.
The information ecosystem is also part of the problem. Mainstream media moves too slowly for threats that evolve by the hour. By the time coverage appears, the attack pattern has already shifted. Federal agencies like the FBI do publish timely alerts, but without wide, clear distribution from MSM, those warnings rarely reach people when they need them.
Tech media is on the other end of the spectrum. There is more coverage, but it’s complicated and difficult to follow. The language is dense, the explanations assume prior knowledge, and the format leans on rapid, bite-sized clickbait videos optimized for attention rather than understanding. Viewers are expected to process complex steps quickly. That is expecting too much from an elderly audience who did not grow up navigating this technology-driven world.
And it’s not just the elderly. There are serious accessibility issues. People like myself, for example, with ADHD, and others with learning disabilities are rarely considered in how guidance is designed.
When instructions are rushed, overloaded, or poorly structured, most people will struggle to apply them under pressure. And in the context of social engineering, where seconds and clarity matter, that gap directly translates into risk.
In the subsequent post, we’ll be breaking down one of the more unsettling phishing trends right now: fake digital invitations from platforms people instinctively trust.
We’ll walk through how to spot them, what to do if you’ve already been caught off guard, and how to avoid falling for them in the first place.


To me who is technologically challanged .... thank you !